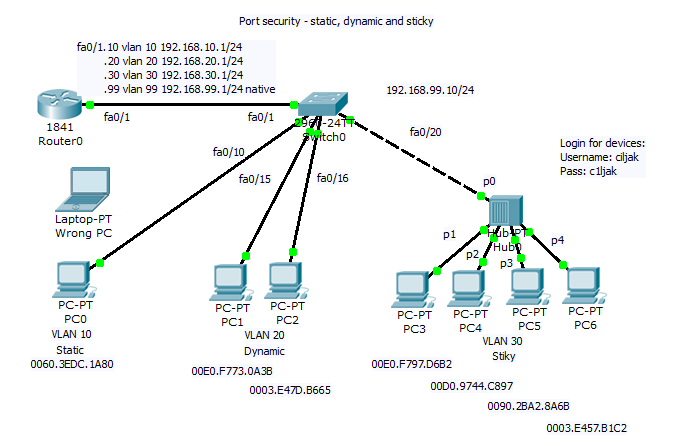
PRACTICAL NETWORK SECURITY CONCEPTS (PART-1) : SWITCHPORT SECURITY. | by oluyede Segun (jr) | Medium

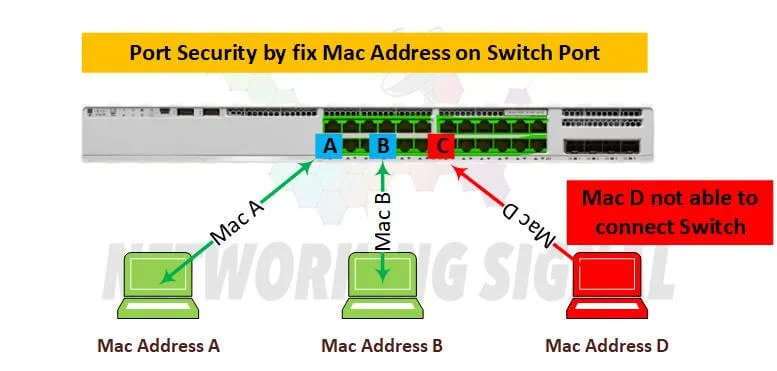
port security:Learn how to secure cisco switches ports using switchport – Learn Linux CCNA CCNP CEH CISSP CISA Penetration-Testing Bug Bounty IPv6 Cyber-Security Network-Security Online
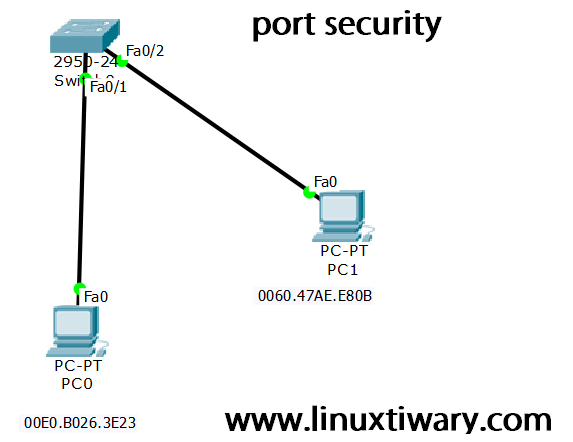
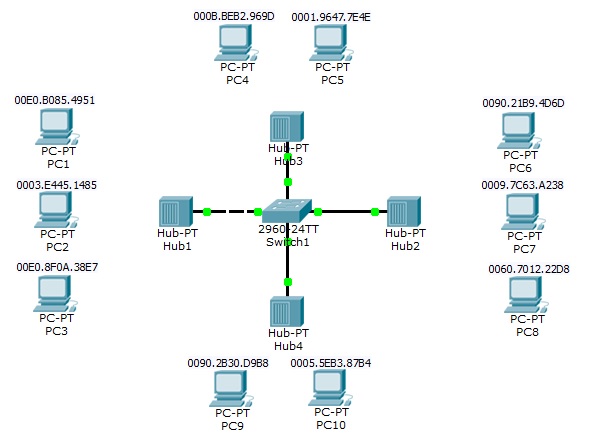
Port Security Configuration on Cisco switch using packet tracer – Learn Linux CCNA CCNP CEH CISSP CISA Penetration-Testing Bug Bounty IPv6 Cyber-Security Network-Security Online
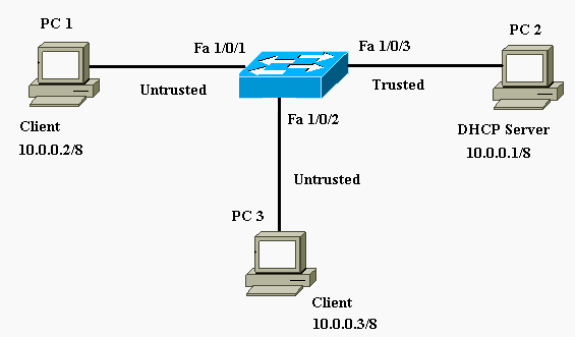
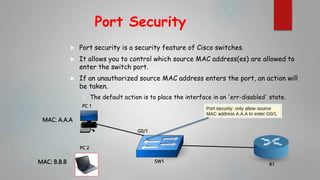
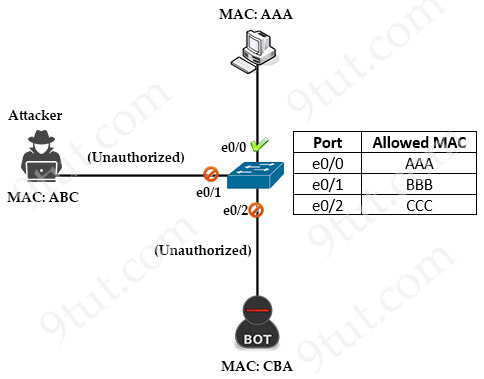
Layer 2 Security Features on Cisco Catalyst Layer 3 Fixed Configuration Switches Configuration Example - Cisco


.jpg)